In an era where our lives are increasingly lived online, a profound and unsettling truth has once again been thrust into the spotlight. A significant digital privacy scandal has been exposed today, sending shockwaves through the tech industry and among users worldwide. This is not an isolated incident but rather a symptom of a much larger, systemic issue within the digital economy. This article will provide a deep dive into the nature of this latest breach, explore the intricate web of data collection, and arm you with actionable strategies to reclaim your digital privacy. The conversation starts now, and your awareness is the first step toward protection.
A. Unveiling the Modern Data Breach: Beyond Simple Hacks
The term “data breach” often conjures images of shadowy hackers in dark rooms bypassing sophisticated firewalls. However, the reality of modern digital privacy scandals is often more nuanced and, in many ways, more insidious. The scandal exposed today likely doesn’t involve a classic “break-in.” Instead, it revolves around the legal, yet ethically questionable, practices of data harvesting, sharing, and exploitation that occur with every click, tap, and scroll.
This particular event centers on the discovery that a vast network of apps and websites has been employing sophisticated tracking pixels and software development kits (SDKs) to collect user data far beyond what is necessary for their functionality. This information, which includes location history, private messages, device identifiers, and even biometric data, was not merely stored for internal use. It was systematically packaged and sold to third-party data brokers, who then created detailed profiles sold to the highest bidders, including advertisers, political consulting firms, and even insurance companies.
The gravity of this situation lies in its scale and the sheer intimacy of the data exposed. We are not talking about email addresses and passwords alone; we are discussing the comprehensive digital fingerprint of millions of individuals, compiled without their explicit, informed consent.
B. The Engine of Exploitation: How Your Data is Collected and Sold
To understand the scandal, one must understand the machinery behind it. Data doesn’t just leak; it is systematically extracted through a complex ecosystem designed for that very purpose.
A. The First Layer: Data Collection Points
Your data is collected at numerous touchpoints:
-
Social Media Platforms: Every like, share, comment, and even the time you spend hovering over a post is recorded.
-
Mobile Applications: Many free apps request permissions they don’t need (e.g., a flashlight app asking for location access) to harvest valuable data.
-
Websites and Tracking Cookies: Cookies follow you across the internet, building a profile of your interests, fears, and desires.
-
Internet of Things (IoT) Devices: Smart TVs, voice assistants, and even connected refrigerators collect data on your daily habits within your own home.
-
Public Wi-Fi Networks: Unsecured networks can be used to intercept your data and monitor your online activity.
B. The Middlemen: Data Brokers and Aggregators
This raw data is worthless on its own. It is sold to data brokers companies you’ve never heard of, like Acxiom, Experian, and Oracle Data Cloud who specialize in cleaning, aggregating, and analyzing this information. They combine your online data with offline records (e.g., public permits, vehicle registrations, magazine subscriptions) to create shockingly accurate consumer profiles categorized by income, health predispositions, political leanings, and life stages.
C. The End User: The Buyers of Your Digital Soul
These refined profiles are then sold to:
-
Advertisers: For hyper-targeted, manipulative advertising.
-
Political Groups: For crafting micro-targeted propaganda and swaying public opinion.
-
Financial Institutions: To assess creditworthiness and insurance risk.
-
Employers: For potential background checks on candidates.
This scandal has exposed a specific, egregious link in this chain, revealing how data meant for one purpose was funneled into this shadowy economy.
C. Immediate Repercussions: The Tangible Dangers of Data Exposure
The “why should I care?” question has a very concrete and frightening answer. The exposure of such sensitive data leads to direct harms:
A. Advanced Phishing and Social Engineering Attacks
With access to your detailed personal information, scammers can craft incredibly convincing phishing emails and messages. Instead of a generic “Dear Sir/Madam,” you might get an email that says, “Hi [Your Name], we noticed an unusual charge at the [Your Favorite Restaurant] you visited last Tuesday. Click here to verify.” The level of detail makes the scam highly effective.
B. Identity Theft and Financial Fraud
With enough data points full name, address, birthdate, mother’s maiden name malicious actors can impersonate you to open new credit lines, file fraudulent tax returns, or drain existing accounts.
C. Reputational Damage and Blackmail
Private messages, search histories, or photos that were never intended for public consumption can be weaponized for extortion and public shaming, destroying personal and professional relationships.
D. Manipulation and Erosion of Autonomy
When entities know your deepest fears, insecurities, and desires, they can manipulate your behavior. This goes beyond showing you ads for shoes you looked at once. It can influence your voting behavior, skew your perception of reality, and exploit psychological vulnerabilities for profit, effectively limiting your ability to make free, independent choices.
D. Fortifying Your Digital Fortress: A Proactive Defense Guide
Knowledge is power, but action is protection. Here is a comprehensive guide to locking down your digital life. You don’t need to be a tech expert; you just need to be diligent.
A. Audit and Reinforce Your Passwords
-
Use a Password Manager: Tools like Bitwarden, 1Password, or LastPass generate and store strong, unique passwords for every site you use. You only need to remember one master password.
-
Enable Two-Factor Authentication (2FA): Whenever possible, activate 2FA. This adds a second layer of security, requiring both your password and a code from your phone or a security key to log in.
B. Become a Permission Skeptic
-
Review App Permissions: Regularly go through the apps on your phone and revoke permissions that aren’t absolutely essential. Does a game really need access to your microphone and contacts?
-
Read Privacy Policies (Selectively): While reading every word is impractical, use your browser’s “Find on page” feature to search for keywords like “third-party,” “share,” “sell,” and “data.”
C. Embrace Privacy-Focused Tools
-
Search Engines: Ditch Google for DuckDuckGo or Startpage, which don’t track your searches or create profiles.
-
Browsers: Use browsers like Brave or Firefox with strong privacy protections. Add extensions like uBlock Origin (ad-blocker) and Privacy Badger to stop trackers.
-
VPN (Virtual Private Network): A reputable VPN (e.g., Mullvad, ProtonVPN, IVPN) encrypts your internet traffic and masks your IP address, making it much harder for your online activity to be tracked, especially on public Wi-Fi.
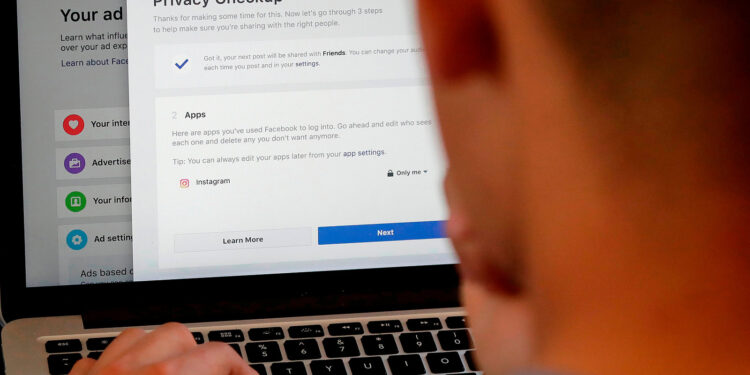
D. Control Your Social Footprint
-
Lock Down Privacy Settings: Regularly check and tighten the privacy settings on all social media platforms. Limit past posts, disable ad personalization, and make your profiles visible only to friends.
-
Think Before You Post: Assume anything you share online is permanent and public, even in “private” messages.
E. Stay Informed and Advocate
-
Subscribe to Security News: Follow reputable sources like Krebs on Security, The Hacker News, or TechCrunch’s security section to stay updated on the latest threats.
-
Support Digital Rights: Consider supporting organizations like the Electronic Frontier Foundation (EFF) that fight for digital privacy rights and lobby for stronger regulations.
E. The Bigger Picture: Demanding Systemic Change
While individual action is crucial, this is a systemic problem requiring systemic solutions. The exposed scandal underscores the urgent need for:
A. Robust and Enforceable Legislation
Laws like Europe’s General Data Protection Regulation (GDPR) and California’s Consumer Privacy Act (CCPA) are steps in the right direction, but they need to be stronger and more universal. We need laws that:
-
Mandate opt-in consent for data collection, rather than forcing users to opt-out.
-
Impose severe financial penalties that actually deter multi-billion dollar companies from violating the rules.
-
Give individuals a private right of action to sue companies that misuse their data.
B. A Fundamental Shift in the Digital Business Model
The current “surveillance capitalism” model, where the user and their data are the product, is fundamentally broken. We must encourage and support alternative models that prioritize user privacy, such as:
-
Freemium models: Where basic services are free, but advanced features require a subscription.
-
Ethical advertising: Contextual advertising (ads based on the page content, not your personal data) is a viable and less invasive alternative.
-
Data minimization: Companies should only collect data absolutely essential for the service provided and delete it immediately afterward.
C. Corporate Accountability and Transparency
Companies must be held to a higher standard of transparency. This includes:
-
Clear, Plain-Language Privacy Policies: Documents that are actually understandable to the average person.
-
Regular and Independent Audits: Third-party audits of their data practices to ensure compliance and build trust.
-
Breach Notification in Real-Time: Informing users immediately when their data has been compromised, not months later.
Conclusion: Your Privacy is Your Right
The digital privacy scandal exposed today is a stark reminder that in the digital world, vigilance is not optional it is essential. It reveals the uncomfortable truth that our personal information is a valuable commodity in a largely unregulated market. However, you are not powerless. By understanding the mechanisms of data collection, recognizing the real-world dangers, and implementing a layered defense strategy, you can significantly reduce your digital footprint and reclaim a measure of your privacy.
Ultimately, this is about more than just avoiding targeted ads; it is about protecting your autonomy, your finances, and your very identity. Let this news serve as a catalyst for change both in your personal habits and in your demand for a more ethical and secure digital future for everyone. The responsibility lies with individuals, corporations, and regulators to build a web that respects its users, rather than exploits them.